Everyone has had that moment when someone they know, who is already on Facebook, sends another friend request. The recipient clicks on the link in the message, only to later see the same person posting, 'Don’t expect friend requests from me, I’ve been hacked.' Or perhaps you're concerned about someone accessing your baby monitor but don't know how hackers do it. Maybe you're the one who has numerous passwords written down and is too afraid to use a password manager. If you answered yes to any of these examples, this article is for you.
Here are my tips and tricks for you to fortify your digital defenses at home and in your personal life.
Facebook Security 101: If you are going to be on social media and not be a victim, you need to know how to protect yourself from cybercriminals. I am sure you have had a moment when someone sends you a friend request or a Facebook message and it looked “sketchy” to you. You didn’t open it, and soon, you see a post about that person getting “Hacked.”
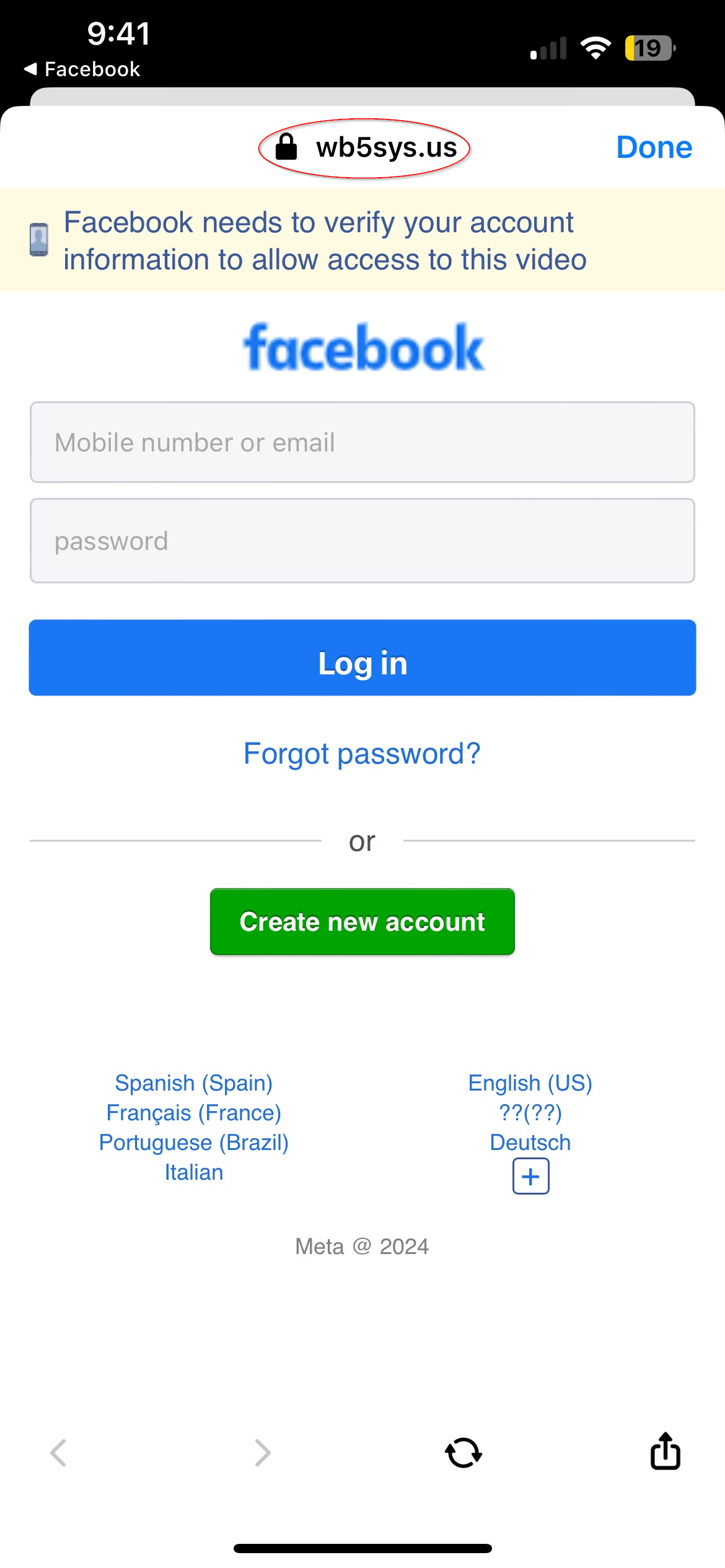
The attack the cyber criminals use is relatively easy to compose. All they need to do is buy an available domain name and hope you don’t notice when you are redirected to a webpage they own but clone Facebook for your credentials to harvest. Got that? Allow me to explain.
The internet operates on something called “DNS” Domain Naming System. If it didn’t exist, it would make your web surfing very difficult. Why do you ask? Well, it’s because every internet site around the world actually has a numerical identifier but uses DNS to make it easier to remember an internet site. An example would be when you search for Amazon.com, you search for Amazon.
If DNS did not exist, you would search for Amazon using a numerical sequence of 104 dot something in the browser, it would make your shopping difficult, and you probably wouldn’t remember the numerical sequence. Welcome to DNS! It’s a love/hate relationship among IT professionals around the world.
The most common attack vector for a cybercriminal to compromise your Facebook account is to send you a friend request. It’s not a real request which is hurtful if you ask me. To make the attack successful, the cybercriminal will buy a domain name, and it can be anything because they are hoping you will not focus on the domain name and only on the pretty Facebook login page you are so fond of seeing every day.
Most of the attacks are in the narrative below. Someone sends you a message about some pictures they found of you. You can either click the link or you can be like me and say, ‘Enjoy the pictures.”
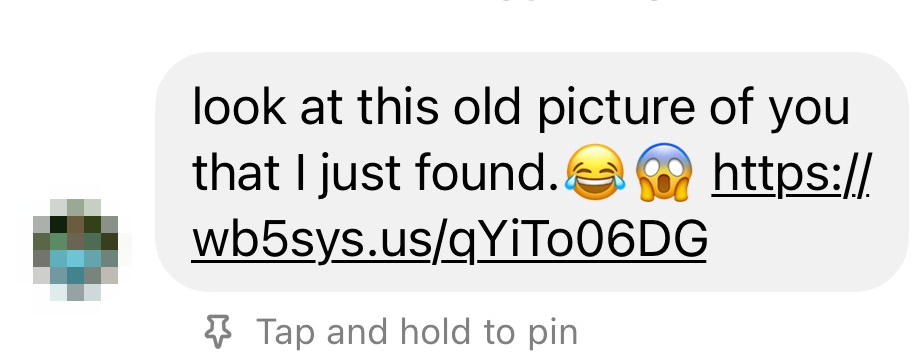
If you are the daring type and actually click the link, it will magically transport you to another page that looks like the Facebook login page. Here is where you will input your username and password so you can log into Facebook…..NO!! You will do no such thing; keep reading this article to protect yourself.
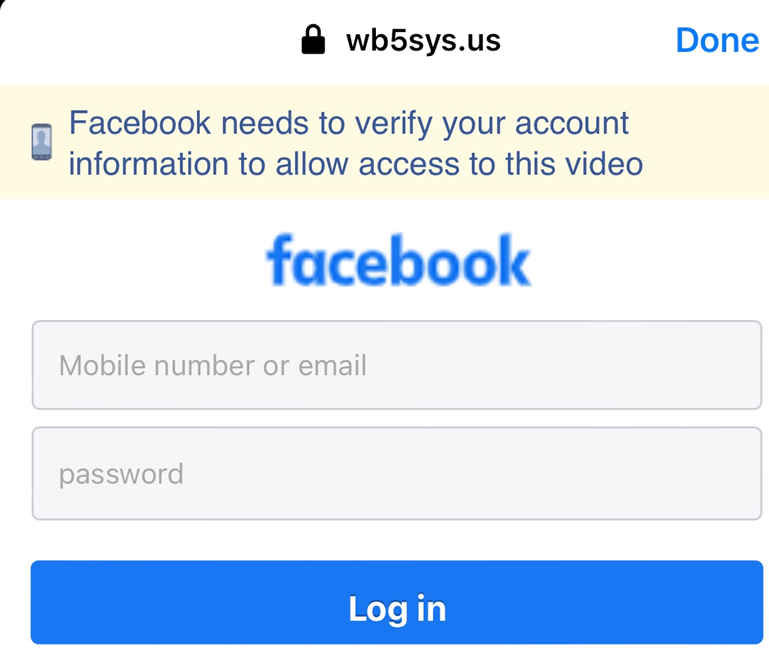
The reason why these attacks are so successful is because the cybercriminal is hoping you cannot read or care about what is so obvious. If we look at the top of the screen, we should see a Facebook where there is a “wb5sys.us.” This is a malicious domain that is owned by the cybercriminal used to harvest your credentials to Facebook. To make it more convincing, they use free software to clone the actual Facebook login page to convince you to input your credentials. So…friend request denied!!!
What can you do to prevent yourself from becoming a victim? You can follow these steps to keep yourself safe.
- Don't accept friend requests from people you don't know or already have on Facebook. Search for their name on your list. Scammers may create fake accounts to friend people so be on alert. Becoming friends with scammers might allow them to spam your timeline, tag you in posts, and send you malicious messages.
- Never click suspicious links, even if they appear to come from a friend or a company you know. This includes links on Facebook (for example: on posts) or in emails. Keep in mind that Facebook will never ask you for your password in an email.
- Enable two-factor authentication. Two-factor authentication is a security feature that helps protect your Facebook account and your password. If you set up two-factor authentication, you'll be asked to enter a special login code or confirm your login attempt each time someone tries accessing Facebook from a browser or mobile device we don't recognize.
The Baby Monitor Is Hacked!
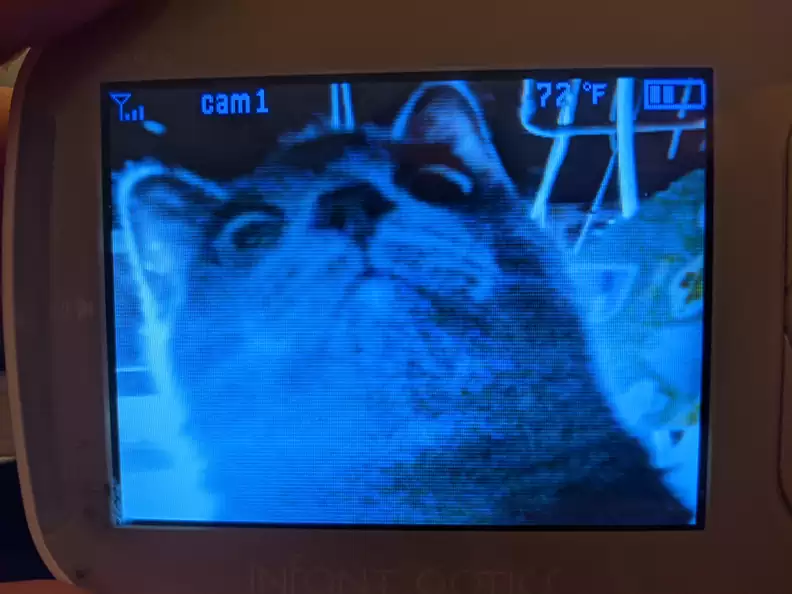
You can usually find an instance of a baby monitor being hacked. It’s something that frightens parents or anyone who requires there be a camera in their family member’s room. Such a story was published by the New York Post titled “I heard a strange man talk to my daughter in her room — our baby monitor was hacked.” The article is about an Australian family who had their VTech baby hacked by an intruder and the intruder was making sounds on the monitor.
Commenters on the parents’ video said the Wi-Fi feature may be to blame for the invasion of privacy. If you are a parent like me, you understand the importance of Wi-Fi-enabled devices. Was Wi-Fi really the catalyst for this story that led an intruder to access the baby monitor? Yes and no. In this example, the parents are using a VTech baby monitor, and we should read the user manual on best practices for WI-FI security.
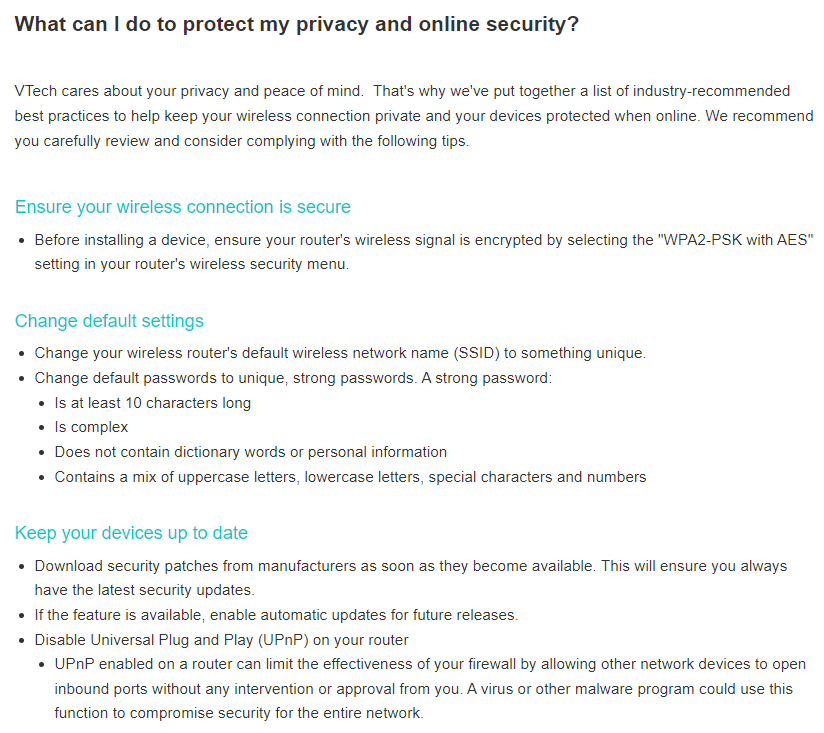
So, if the family in the article followed all the steps located in VTech’s Wi-Fi security recommendations, how did the attacker gain access to the baby monitor? Elementary my dear Watson. There are a few scenarios, but I will use the top two that I can think of for a successful attack.
Scenario #1 The Wi-Fi the VTech Baby Monitor Was Using Didn’t Have a Password.
For this attack to be successful, the attacker would have to achieve the following items first.
- Be in close proximity to the family’s house to access the Wi-Fi.
- Know the family’s Wi-Fi SSID. SSID means “Service Set Identifier” or what you call your Wi-Fi network at home. There are many tools that are used for the reconnaissance of public SSIDs. WiGle is an example of a reconnaissance tool for SSIDs. Wigle is one more tool that an OSINT investigator can use to attempt to locate a target. Given the name (SSID) of the AP the target has connected to in the past, (possibly from their registry) or interpolating their phone tethering name, we may be able to precisely determine their location.
- Accessing the correct Wi-Fi SSID and joining the network.
- Scan the network to find devices that are currently on the network. Since I have a VTech baby monitor, I will demonstrate what that looks like. In order for the attacker to gain access to the VTech baby monitor, the attacker has to identify the IP address or the name of the baby monitor. This is possible through various network scanning software tools that are available for mobile phones for scanning on-the-go techniques.
After gaining access to the network, I use a network scanner to see what network devices are available to access. The picture below shows that I do see that there is a VTech baby monitor available but it does not have any communication ports available for me to connect to. Even though I am not able to access the baby monitor directly, I know the name of the baby monitor. This is beneficial because since I am on the network now, I can install the app for VTech and add the monitor to my device list.
This will give the attacker access to the baby monitor, and they will be able to talk through it. Giving the parent and child years of needed therapy.
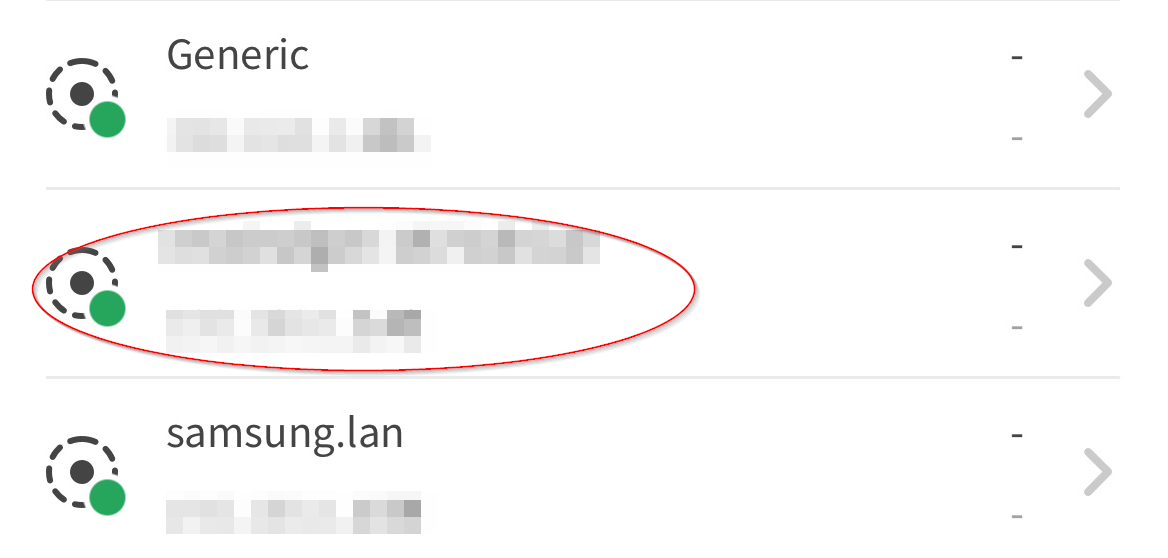
Since there are no open ports on the baby monitor for me to communicate through, I downloaded the VTech baby monitor app so I could use the baby monitor. VTech has a website that has a wonderful “How To” section on how to add a device to your app.
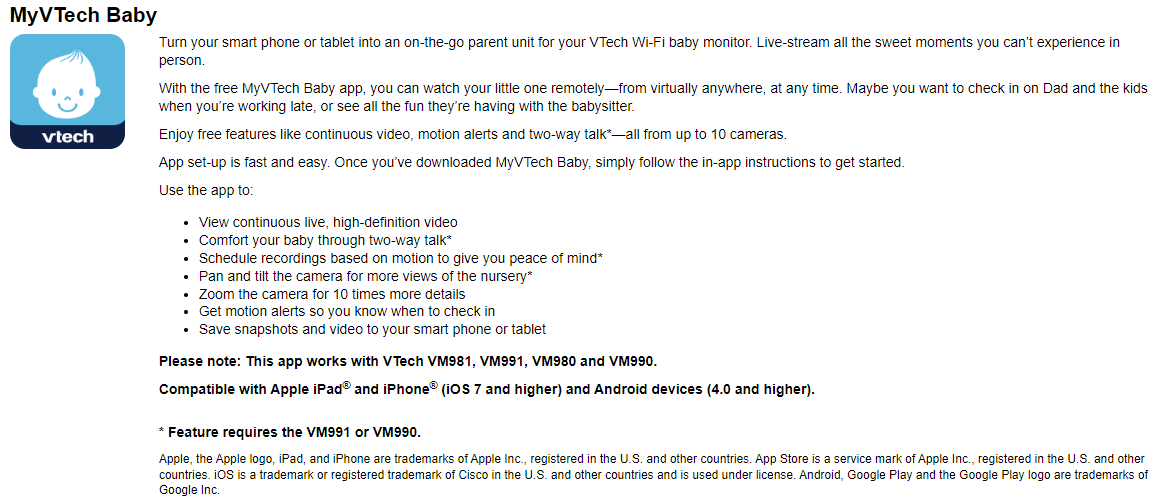
After downloading and installing the app, you can scan the network and search for the baby monitor. After you find the baby monitor, you can add it to your device list. This gives the attacker the ability to access the baby monitor and interact with it.
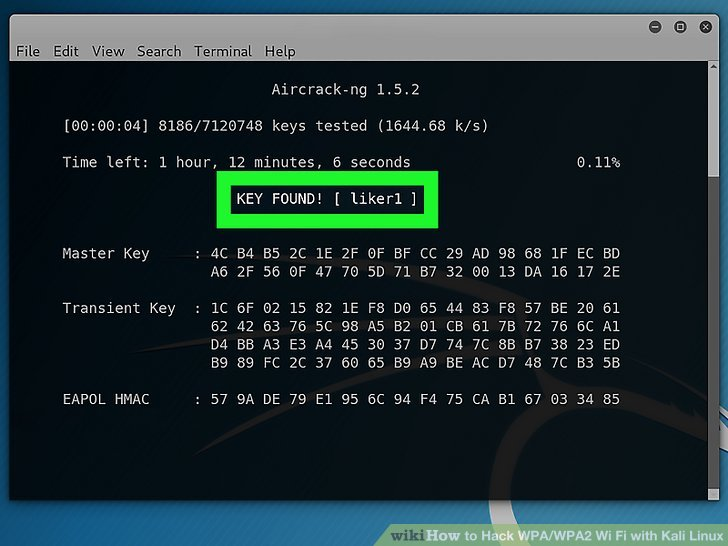
Scenario #2 The Attacker Was Able to Capture the Wi-Fi Password Using Wi-Fi Sniffing Tools.
This scenario is more involved than the first example and requires more technical experience to execute. The attacker will need to be in close vicinity to the Wi-Fi they wish to attack. In order to capture the password for the Wi-Fi, the attacker will need a few items.
- An extra Wireless adapter
- Kali Linux or choice OS
- Aircrack-NG and Aireplay-NG
For this attack to be successful, the attacker will want to capture a device successfully connecting to the network. We call this the handshake aka the password. The best way for us to accomplish this is to run an attack against the connected device and kick it from the network. It will attempt to reconnect, allowing us to capture the handshake. After the attacker captures the handshake, they will then need to crack the password with a wordlist, and we know passwords can be weak.
What can you do to prevent yourself from becoming a victim? You can follow these steps to keep yourself safe.
- Use the hide your SSID option that is available on every router. This means your SSID will not be listed when someone is in your neighborhood scanning for open networks.
- Use a strong password.
Follow the VTECH Wi-Fi security recommendations. 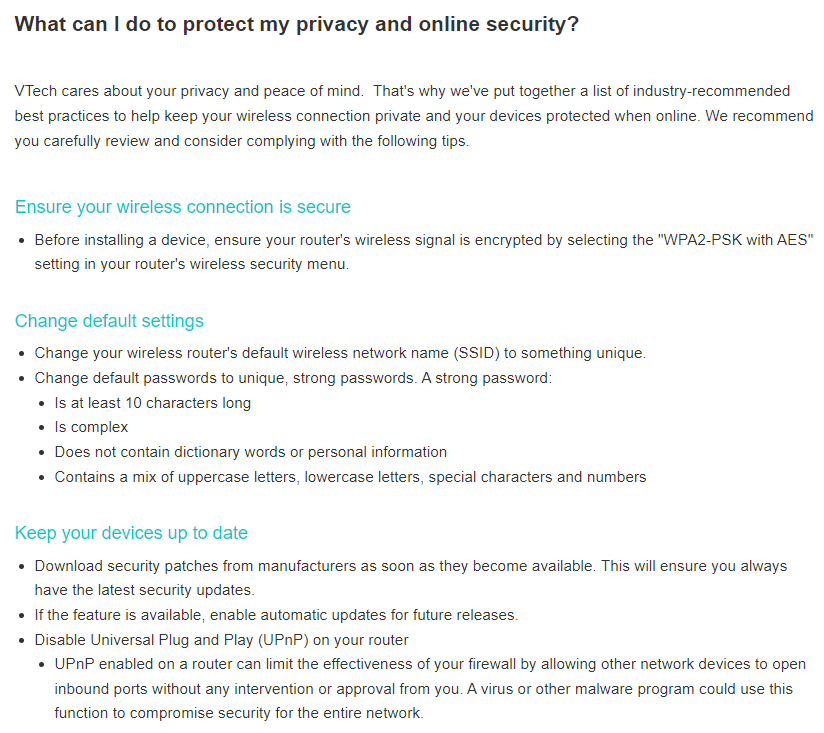
What’s the Password?… Never Mind I Know It.

Everyone receives an email or alert at some point about their password being seen on the “Dark Web.” Do not be discouraged because it’s just a password, and it can be changed or maybe you don’t use the account associated with the password. Sometimes, it’s the password you use for Facebook, and you start to sweat over it. Well, towel off because you look awful, and people are staring at you.
How do you create a secure password, remember it, and utilize it effectively when you want? There are numerous websites devoted to creating new passwords for you to use. Let’s face it, passwords are an out-of-date concept, but we still need them. A password should be 8 characters or more containing at least a number or symbol. You can even add spaces if that helps. The longer the better but most importantly, you need to remember it. How do you accomplish this task? Strap in, and let me show you.
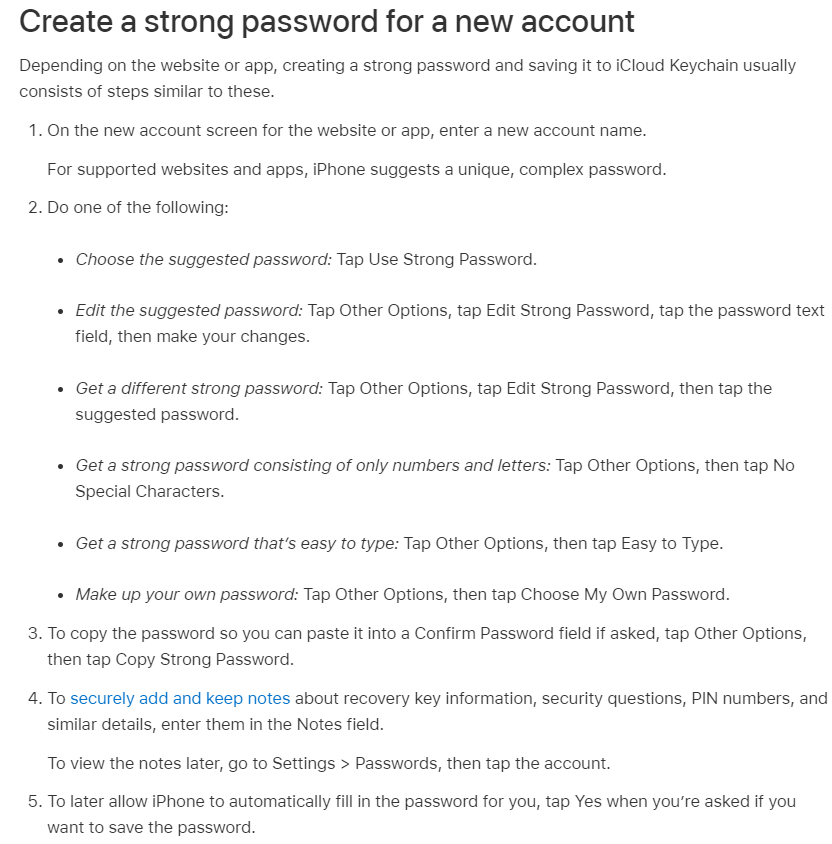
For secure password generation, you can use a variety of tools. For the sake of time, I will name two and show you how they work. Since most of the world is in a constant mobile state, we will first look at the Apple IOS password built-in generator. The great feature of the Apple password generator is you can use FACE ID to automatically sign into the accounts you create the passwords for. You will not need to remember passwords using this feature.
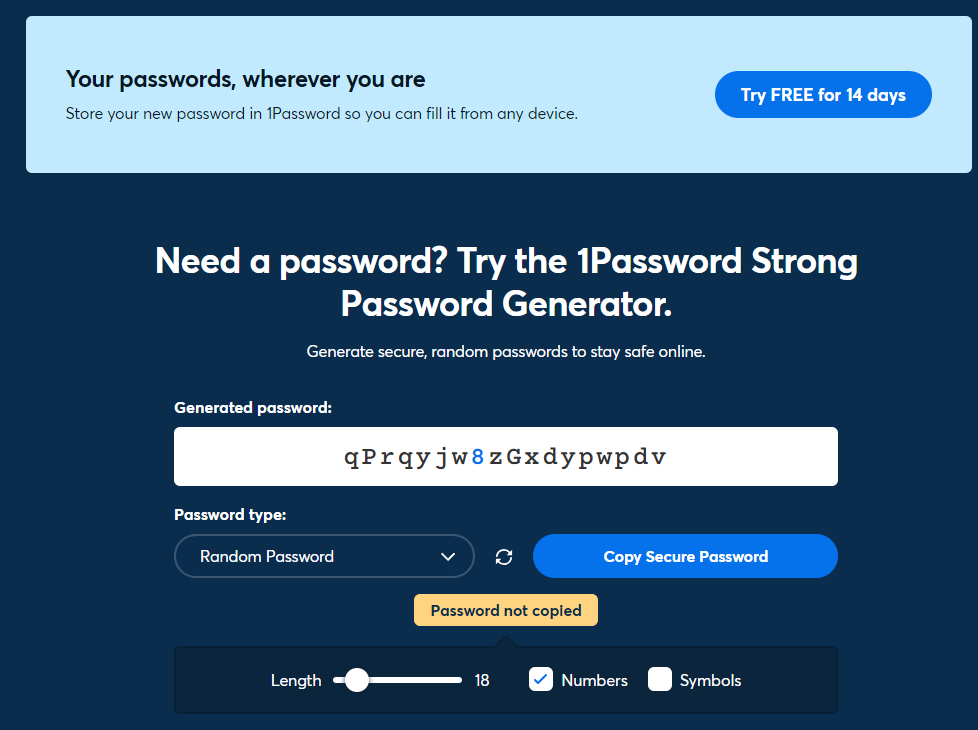
For anyone who does not have an iPhone, I would suggest using a webpage to create a secure password. I would recommend the 1Password generator. When you use the 1Password generator, you have the ability to create a password matching all criteria needed.
- Random password
- PIN
- Memorable password
- Various lengths, numbers, and symbols.
You also have the ability to copy and paste to whatever password manager you are using.
Keep It Secret…Keep It Safe.

What does someone do with so many passwords to so many websites and apps? Well, you need a manager to keep everything so you don’t have to remember it. To quickly summarize, using the same password for every website and app is an open invitation for hackers to access all of your accounts. That's because passwords regularly leak, and a leaked password on one site can give hackers access to all your other accounts if you use the same password everywhere.
It's best, then, to use a totally different password on every site, but no human being can remember that many passwords. My suggestion is the password manager on your iPhone. One of the best “How to guides” is an article published by Forbes called “How To Save Passwords On iPhone (2024 Guide).”
Alexa! What Are You Doing?
As someone who makes a living as a tech safety expert, I have been asked if Alexa can be hacked. I always answer with this: If it’s connected to Wi-Fi, then it is always possible to a degree. There have been some articles about exploiting the Echo Dot but most of them require the attacker to take the Echo apart and solder some parts and then get you to purchase the Echo or install it on your network. Here are some scenarios and safe practices about the Echo Dot.
The Weird Ways Your Amazon Echo Can Be Hacked
-
Voice Squatting - One of the biggest security risks around Alexa right now is fake skills – also known as Voice Squatting. Researchers were able to register skills that sounded like popular incumbents, using accents and mispronunciations to illicit unwitting installations. The study created Alexa skills and Google Actions that hoovered up slight nuances in people’s commands. This exploit has been closed by Amazon.
However, it’s still a good job to monitor the skills you have installed via the Alexa app. With some skills looking for payment information and boasting the ability to hook up with other services, and the low barrier for installation of skills, this is a problem that might not go away too quickly.
-
The connected home hack - You can set Echo up as the center of your smart home array. It’s easy to do, and we certainly wouldn’t advise anyone against it. It is worth bearing in mind, though, that Alexa will talk to anyone. Amazon’s virtual assistant doesn’t come with any kind of voice recognition authentication constraints.
So, in theory, if you put Echo within earshot of the outside world, then a stranger standing near your windows, or your front or back door, could start making requests for Alexa. So, they could turn your lights off and on, tamper with your heating or, even, possibly, unlock your doors.
- The chassis hack: This is not what I paid for - It looks like an Echo, it sounds like an Echo, but is it really an Echo? It would be possible for someone to design their own version of a voice assistant with entirely different and evil ends and then just whack it inside an Amazon Echo shell and sell it to an unsuspecting punter. It would be easy enough to record Alexa’s voice by asking a genuine Echo to repeat phrases for you, but could you really record enough responses to keep the user from your ruse?
-
Voice history hack - This one’s an extension of ‘voice squatting’ that was discovered by cybersecurity firm Check Point Research in August 2020 but has been fixed by Amazon. CPR found that your entire voice history could be made available to a hacker with just one click of a fraudulent link that surreptitiously installed a rogue skill.
There’s not a huge amount of value in nicking hours and hours of recordings of you setting timers and turning your lights on and off, but the data could potentially be used to trick voice verification systems and even create audio deepfakes. When it comes to smart devices such as the Alexa Dot, if there is a fear of having a device steal sensitive information or listen in on your conversations, there are some safeguards that will help.
- Change Default Credentials during setup - The first step is to change any default usernames and passwords. For example, if you’ve just bought a new smart camera, make sure to set a strong, unique password that isn’t easily guessable. Most of these devices are available through the internet and attackers always attempt to log into them with default credentials or using large password dictionaries.
- Regularly update device firmware - Something that happens often is that the firmware that your device shipped with is already outdated by the time you set it up. Manufacturers often release feature updates and security fixes. Ensure your IoT devices are set to update automatically or regularly check for updates. This is a preventative measure to keep your devices healthy and secure.
- Secure your Wi-Fi network - An unsecured Wi-Fi network is a welcome sign for cyber intruders. Use strong Wi-Fi encryption (like WPA3), set a robust Wi-Fi password, and consider setting up a separate network for your IoT devices. This way, even if one device is compromised, it won’t expose your primary devices, such as laptops and smartphones.
- Disable unnecessary features - IoT devices often come with features that you might not use but could pose security risks. For example, if you never use voice commands on your smart TV, consider disabling the microphone feature.
- Keep an eye on your device - Enhance your home security with a solution at the router level to manage, monitor, and protect devices from network-level exploitation via a smartphone app. It is a smart world that we live in, and we need to make smart choices when it comes to living in the digital landscape. I hope these tips can help secure and fortify your digital defenses.
